The Truth Behind Counterfeit Stock — The Local Artisan Guide

How Possibly Fraudulent and Forged Indigenous Art Ends up in Museums
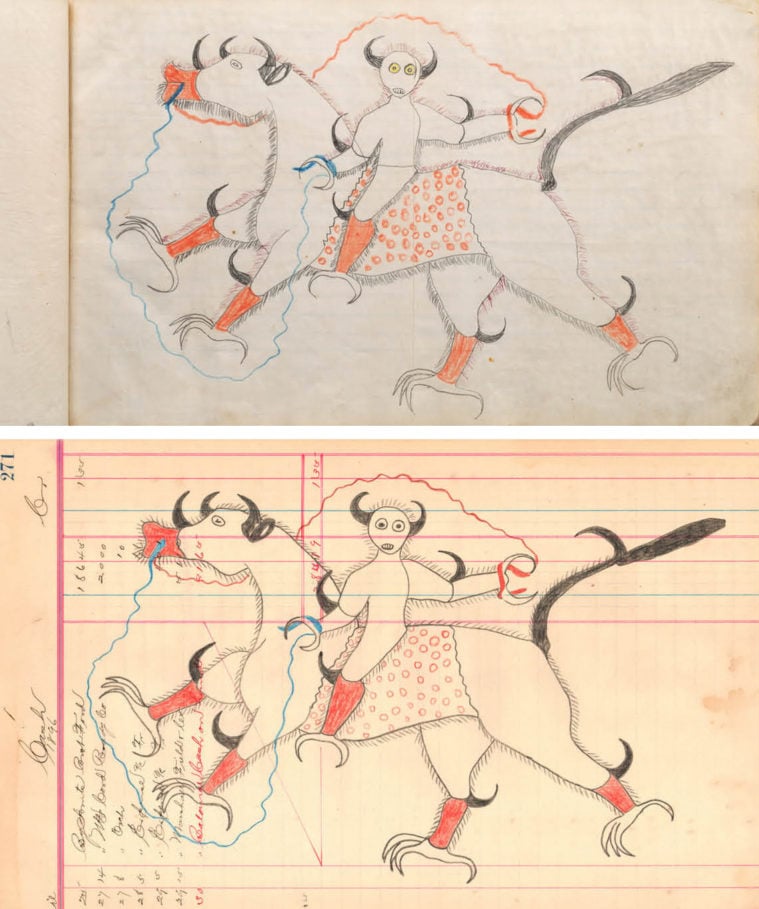
How Possibly Fraudulent and Forged Indigenous Art Ends up in Museums

Microsoft Office Vulnerabilities Used to Distribute Zyklon M
contrast-sets/quoref/quoref_original_subset_20191206_merged.json
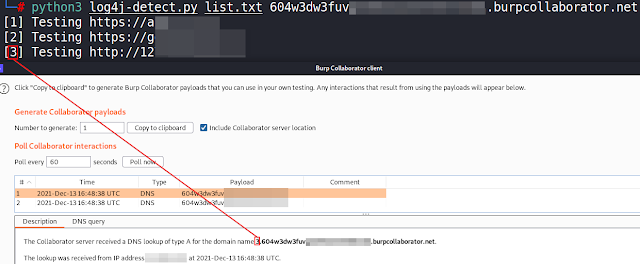
Log4J-Detect - Script To Detect The Log4j Java Library Vul
reveal-community-ranking/visualizationModule/jsons
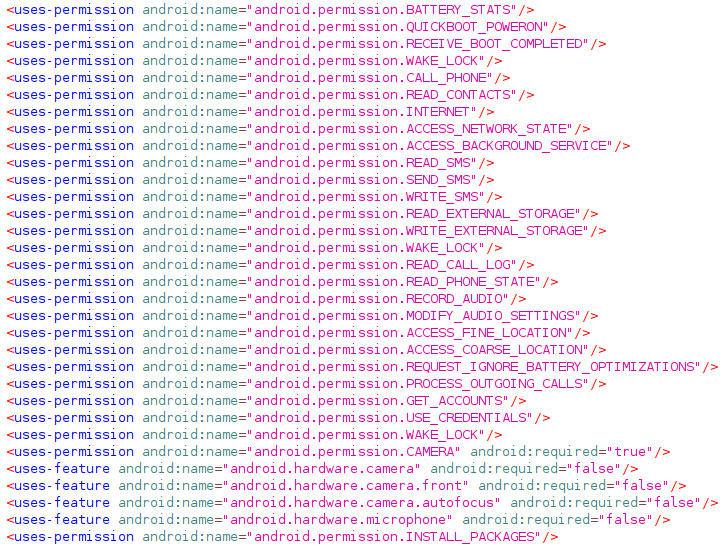
LodaRAT Windows Malware Now Also Targets Android Devices
Grossman LLP, Art Law Blog
The Ultimate Counterfeiter Isn't a Crook—He's an Artist

U.S. Cyber Command Warns of Ongoing Attacks Exploiting Atlas

The Ultimate Counterfeiter Isn't a Crook—He's an Artist
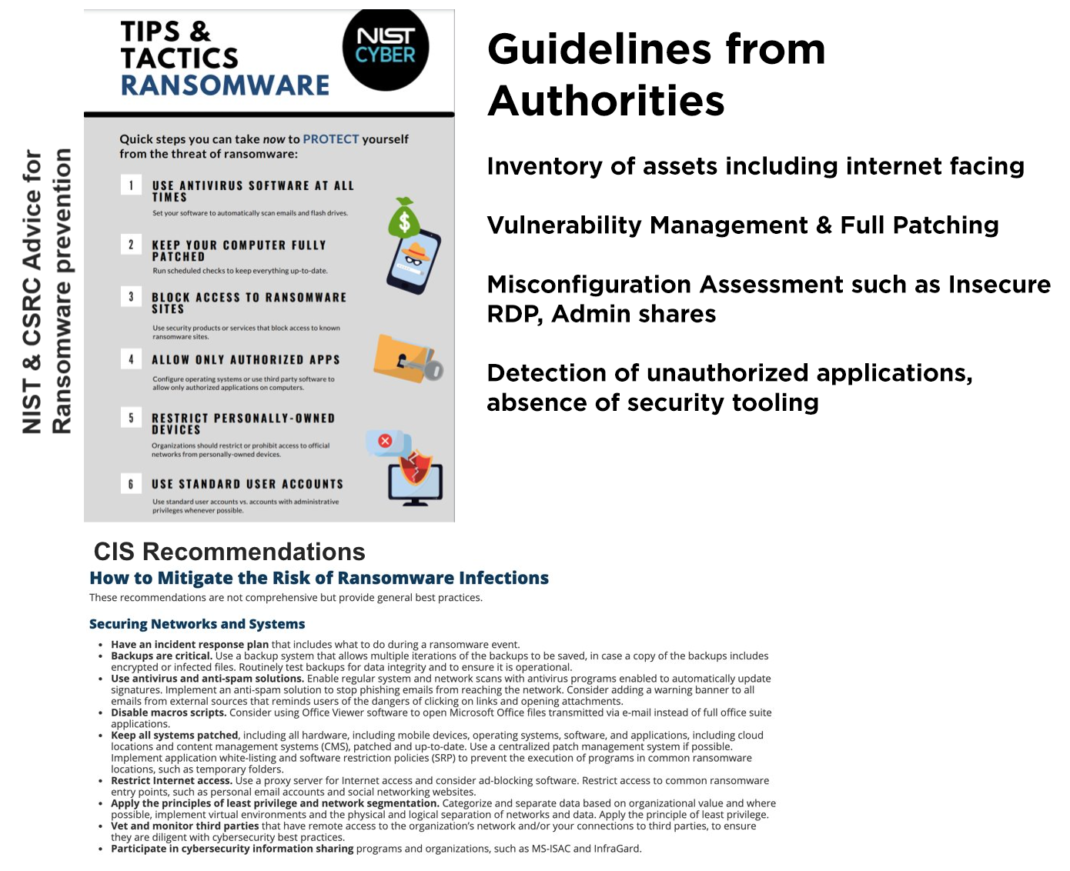
Assess Your Risk From Ransomware Attacks, Powered by Qualys
Last Years Open Source - Tomorrow's Vulnerabilities
coding-challenge/events.json at master · hangtime/coding-challenge
The Truth Behind Counterfeit Stock — The Local Artisan Guide
- Best Price $ 193.50. Good quality and value when compared to danemintl.com similar items.
- Seller - 775+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton LV SHAPE PATCHWORK BELT 40mm 95cm/38”32uk 100%Authentic
Buy It Now 9d 7h -

LOUIS VUITTON Palm Springs MM Monogram Canvas Backpack Brown
Buy It Now 7d 16h -

Louis Vuitton 2009 Pre-owned Speedy 30 Graffiti Handbag
Buy It Now 8d 22h -

Louis Vuitton Rainbow Shirt Worn a dozen times - Depop
Buy It Now 12d 16h -

Pin on Products
Buy It Now 22d 12h -

Louis Vuitton MANHATTAN PM Monogram Canvas M40026
Buy It Now 25d 13h -

How To Authenticate a Louis Vuitton Pochette Bag
Buy It Now 19d 13h -

WeddingFavorites Pattern Pajama Shorts
Buy It Now 26d 15h -

Beauty fans are running to Zara to pick up a perfume dupe that's
Buy It Now 19d 10h -

Cintos Louis Vuitton Original no Brasil com Preço de Outlet
Buy It Now 19d 19h -

Strathberry
Buy It Now 10d 18h -

Louis Vuitton Monogram Toiletry Pouch 26 - Brown Cosmetic Bags, Accessories - LOU798095
Buy It Now 19d 10h -

Smythson Ho Ho Ho! Wafer Notebook, Red
Buy It Now 21d 10h -

The History Of Van Cleef & Arpels
Buy It Now 25d 16h -
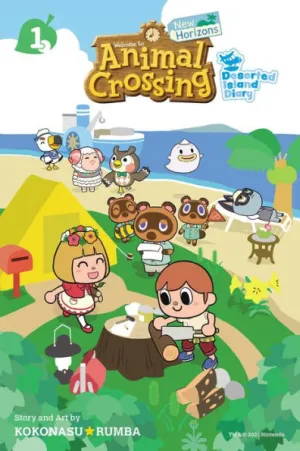
Animal Crossing: New Horizons, Vol. 1: Deserted Island Diary by
Buy It Now 14d 17h -

Virgil Abloh Designed and Signed Louis Vuitton 'LV I (RED) Trainer' Prototype, By “Virgil”, Louis Vuitton & (RED), 2021
Buy It Now 8d 8h -

BRATZILLAZ BRATZ doll purse WICKED purple gold HEART rope handle handbag chain
Buy It Now 27d 20h -

HERMES KELLY 28 STAMP H BLUE JEAN, Luxury, Bags & Wallets on Carousell
Buy It Now 19d 12h -

Paris Las Vegas - Burgundy Room Review
Buy It Now 23d 15h -

Buy PRE OWNED LOUIS VUITTON BAGS, WALLETS AND ACCESSORIES Online
Buy It Now 26d 18h -

Louis Vuitton Félicie Pochette Ebène Damier Ebene
Buy It Now 19d 11h -

Zapatos para Hombre
Buy It Now 24d 14h -

Introducing the Louis Vuitton City Steamer Bag - PurseBlog
Buy It Now 17d 7h -

Louis Vuitton Vanity PM Monogram Reverse autres Toiles Monogram
Buy It Now 6d 5h
