LuxITGirl on Instagram: ““If you're gonna make connections which are innovative you have to not have the same bag of exp…
$ 1967.00 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns
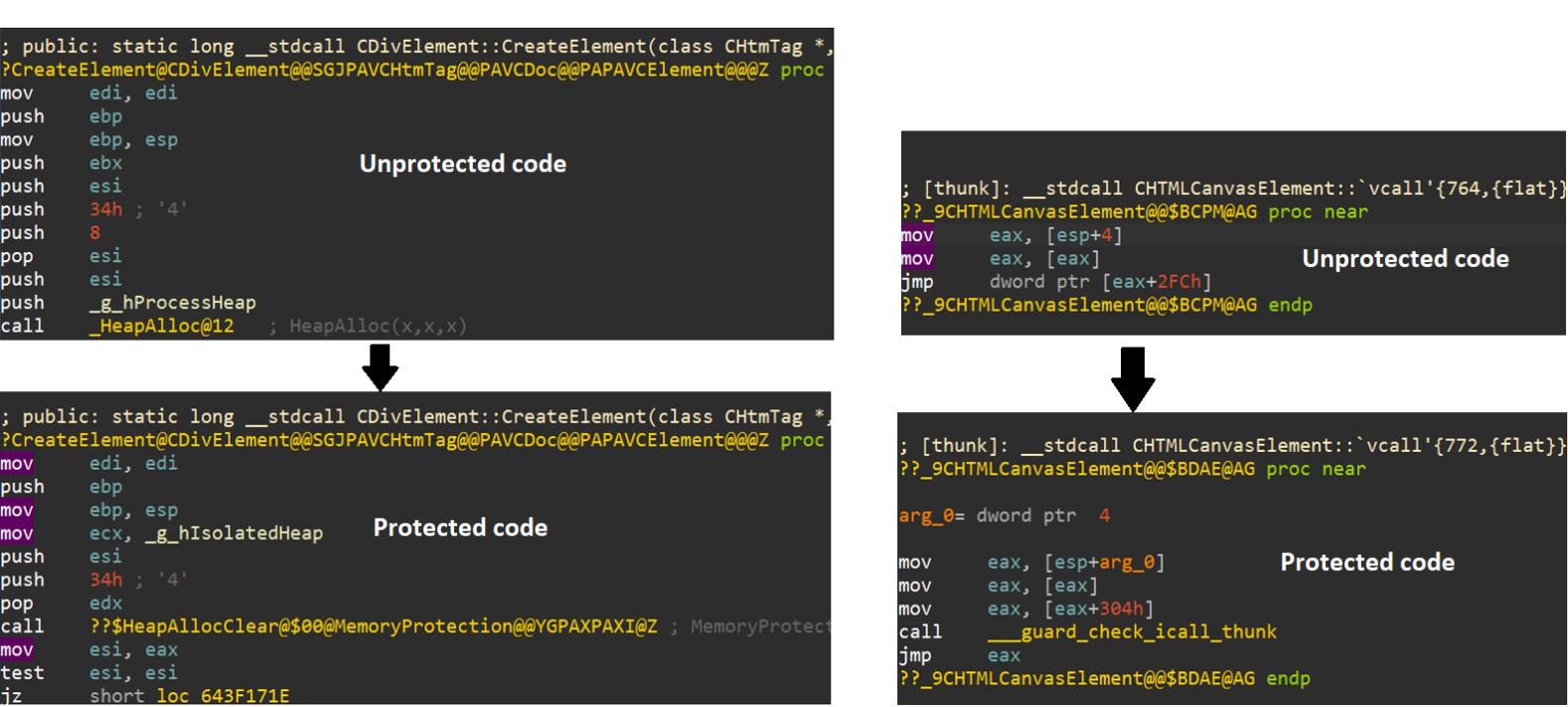
Beyond Memory Corruption Vulnerabilities – A Security Extinc - vulnerability database

Impacket and Exfiltration Tool Used to Steal Sensitive Infor - vulnerability database
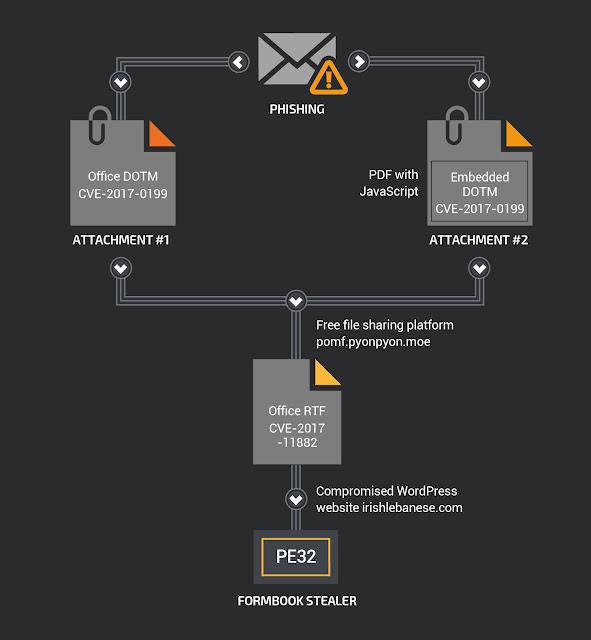
My Little FormBook - vulnerability database

Microsoft Office Vulnerabilities Used to Distribute FELIXROO - vulnerability database
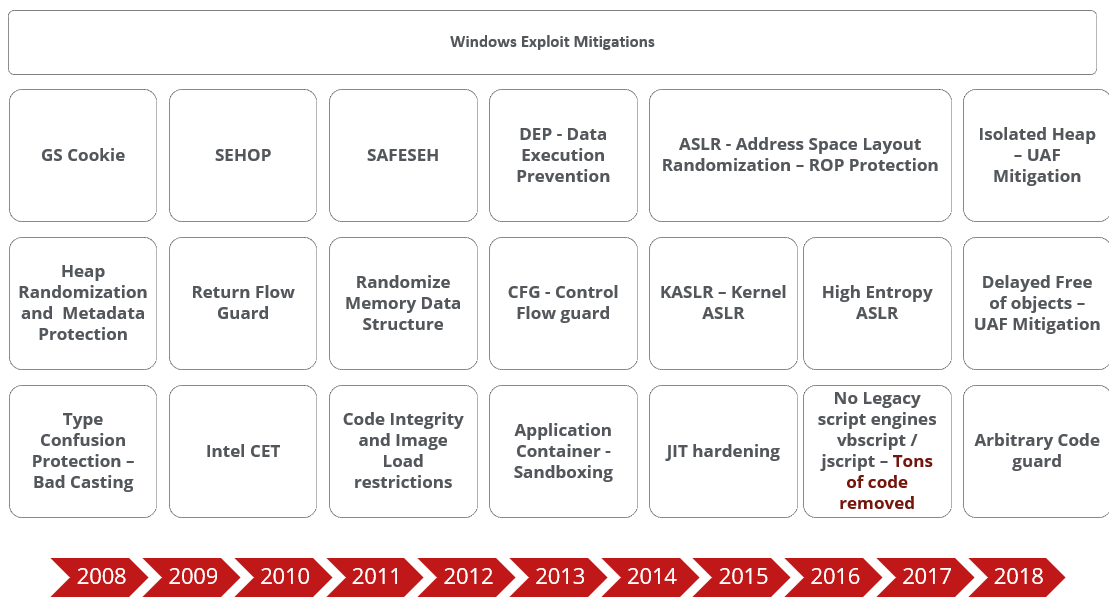
Beyond Memory Corruption Vulnerabilities – A Security Extinc - vulnerability database
LuxITGirl on Instagram: ““If you're gonna make connections which are innovative you have to not have the same bag of exp…
- Best Price $ 1967.00. Good quality and value when compared to danemintl.com similar items.
- Seller - 337+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-
LV Montsouris PM Backpack : New Release 2020
Buy It Now 18d 23h -

Louis Vuitton Louis Vuitton Damier Lv Stories Portefeuille Clemence Round Long Wallet N60147 Brown Auction
Buy It Now 16d 10h -

Bags, Tory Burch Neverfull Style Bag
Buy It Now 2d 9h -

Louis Vuitton Light Style LV Air Jordan 11 Shoes - Banantees
Buy It Now 8d 9h -

Mink Hoody - Ready to Wear
Buy It Now 11d 13h -

Louis Vuitton Coussin Bag 2021 Ford
Buy It Now 11d 21h -

Authentic vs. Fake: Louis Vuitton Trademark Stamps - Academy by FASHIONPHILE
Buy It Now 26d 16h -

Louis Vuitton Monogram Mini Sac HL Speedy with LV Crossbody Strap
Buy It Now 6d 9h -

Louis Vuitton Bumper Pallas iPhone 13 Pro Case
Buy It Now 21d 22h -

8 Best Louis vuitton bandeau ideas louis vuitton, louis vuitton bandeau, vuitton
Buy It Now 12d 5h -

LOUIS VUITTON Monogram Delightful GM 1282016
Buy It Now 24d 14h -

Louis Vuitton Monogram Harness
Buy It Now 20d 18h -

Louis Vuitton 2009 Checkered Shoulder Bag - Farfetch
Buy It Now 9d 7h -

Tanya's Death in 'The White Lotus': Jennifer Coolidge Reacts
Buy It Now 2d 14h -

Introducing the Louis Vuitton Wild at Heart Collection - PurseBlog
Buy It Now 19d 5h -

SLOW RELEASE UTILITY HARNESS – GabriellaMarinaGonzalez
Buy It Now 8d 18h -

LOUIS VUITTON Monogram Eclipse Explorer Bumbag 1193336
Buy It Now 13d 9h -

Anushka Sharma Net Worth & Bag Collection Can Make Everyone
Buy It Now 17d 9h -
Pre-owned Louis Vuitton Black Knit Fabric Aftergame High-top
Buy It Now 3d 18h -

Louis Vuitton - Never Been Worn Empreinte 18 karat Bangle Box French Yellow Gold
Buy It Now 25d 6h -

Nike Air Force 1 Mid '07 LX NBHD Men's Shoes
Buy It Now 6d 22h -

3mm Platinum Ball Earrings Studs JL PT E 182 –
Buy It Now 27d 18h -

Vintage Louis Vuitton Keepall 55 Monogram Canvas with Bandoulière shoulder strap For Sale at 1stDibs
Buy It Now 25d 22h -

Louis Vuitton Zipper Organizer Damier Graphite Wallet Used (6243)
Buy It Now 23d 15h

